How to make full use of threat intelligence technology to effectively monitor sensitive data leakage is an urgent problem to be solved in the integration and development of data security in the emerging fields. Lei Chenglin, deputy general manager, shared the innovative practical experience of Fengtai Technology in sensitive data leakage threat intelligence monitoring at the sub-forum on the integration and development of emerging fields.
Over the years, Fengtai Technology has continued to study industrial Internet security monitoring technology, and has in-depth accumulation in SCADA, PLC, power system, environmental protection monitoring, water conservancy system, medical system, vehicle networking, industrial data real-time database, etc. At present, it has the ability to build real-time monitoring and analysis of leaked industrial data and improve data security risk control and disposal capabilities in the industrial field. Minimize user exposure to attacks.
He said that the particularity of the industrial industry determines that the security of industrial data is closely related to the operation safety and production safety of industrial enterprises, and the data in the industrial field involves many subjects, many types and many formats, and the industrial data is interoperable among the links of research and development, production, management, operation and maintenance, and operation within the enterprise, which involves equipment manufacturers, industrial enterprises, platform enterprises, service providers and other parties. Any link is prone to the risk of sensitive data leakage, and once sensitive data is leaked, It may include class system technical scheme, design drawings, internal address book, special software installation package, system image, control system engineering files, system source code, business point table, business process flow, business process parameters, sensitive production materials, user information and sensitive business data.
Users want to monitor the data that has been leaked or has potential leakage risks, they can start from six aspects: industrial privacy data mapping, industrial data asset mapping, traditional data asset mapping, information and innovation data asset mapping, industrial sensitive data counter-mapping monitoring, and multi-data security intelligence collection, to reduce enterprise attack exposure and improve data security risk disposal capabilities.
Glory and power coexist
In order to improve the level of network and data security and promote the high-quality development of the industry, the Ministry of Industry and Information Technology organized the “Cast Network 2022” security drill. Fengtai Technology won the title of “Cast Network 2022” network security drill outstanding technical support unit of the Ministry of Industry and Information Technology.
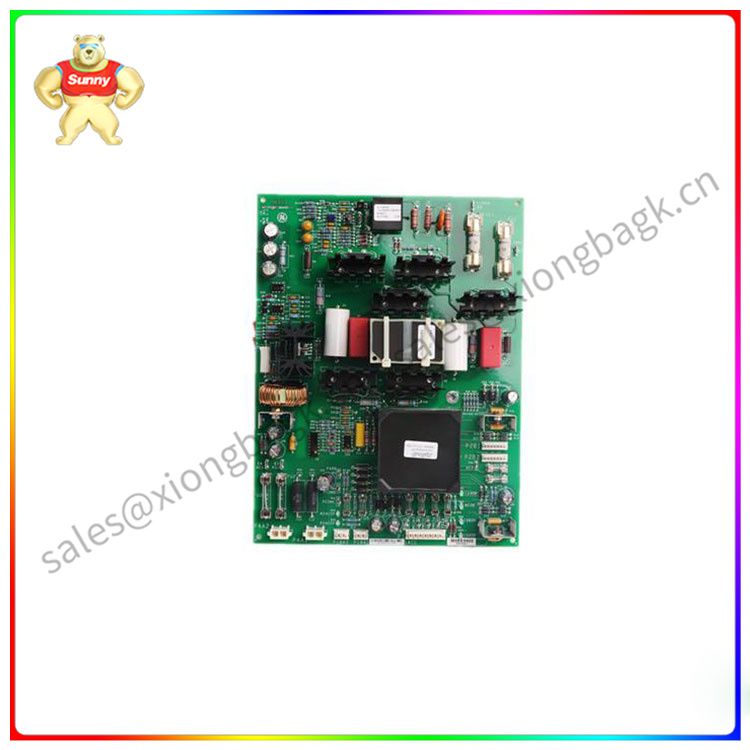
IS210AEPSG1AFC
The “Cast Network 2022” network security drill was coordinated by the Network Security Administration of the Ministry of Industry and Information Technology, and organized by a number of affiliated units. Through sandtable exercise, real network attack and defense, remote penetration, security testing and other forms, a comprehensive and all-field network security real network reality drill was carried out. The comprehensive inspection has improved the protection capability of key industries and typical scenarios in the industrial and information fields, blocked a number of hidden cybersecurity vulnerabilities, enhanced the level of major risk prevention, improved the emergency collaborative work mechanism, and effectively strengthened the comprehensive cybersecurity guarantee capability in the industrial and information fields.
Fengtai Technology industrial network range platform, based on virtualization technology and with comprehensive and accurate assessment method as the core, integrates competition operation and maintenance, competition problem management, attack and defense visualization, assessment and selection, for professional, scientific, comprehensive and accurate evaluation and talent selection. At the same time, the platform can also provide a real industrial simulation environment. Comprehensive simulations of key information infrastructure industries, including steel, petrochemical, power, and transportation, show the real physical equipment, network composition, and process flow of different industries. Starting from actual combat, it comprehensively improves users’ ability to analyze industrial control security risks, exploit vulnerabilities, respond to emergencies and analyze incidents, so as to enhance users’ ability to protect critical information infrastructure.
Building laboratories, supporting industrial control safety competitions, releasing industry system platforms and solutions, the exploration of industrial information security is not yet flat, Fengtai Technology is determined to forge ahead while focusing on industrial information security, with a truth-seeking and pragmatic attitude, to provide more value for users, for the industry, and contribute to the development of the national digital economy.
















